Privacy incidents don’t just trigger legal work. They trigger retention problems. If you want to prevent churn from privacy incidents, you need to treat the conversations around them like high‑stakes CX moments, not checkboxes. Sounds obvious. It’s usually not how it runs in the wild. Legal scrambles. CSMs find out late. Nobody’s checking whether the message matched what the customer actually said.
Let’s pretend you could see every hint of privacy risk, across every ticket, without waiting for a post‑mortem. You’d spot the patterns, fix the root causes, and talk to customers with receipts. Same thing with renewal risk, by the way. It hides inside free‑text. If you don’t turn that into metrics you trust, you’ll argue anecdotes while customers quietly leave.
Key Takeaways:
- Build a custom “privacy‑mention” metric, map raw tags to clear privacy drivers, and validate on real tickets
- Prioritize fixes with a simple ARR x churn‑risk x sentiment model, so work follows dollars
- Use three legal‑safe outreach templates you can test right away, and measure lift
- Prove impact with a tight measurement plan, including incident and cohort windows that stand up in reviews
- Operationalize with saved views, lightweight automation, and evidence bundles for leadership
Privacy incidents are retention problems, not legal chores
Privacy incidents drive churn because they shake trust, and trust loss shows up in renewal math. Legal must act, but CX owns the fallout that customers feel. Treating privacy like CX means measuring signals in conversations, prioritizing by value at risk, and closing the loop fast with proof. One example, a billing export bug triggers privacy mentions that spike churn risk in mid‑market accounts.
Where churn hides in privacy conversations
Churn hides in small phrases, not just explicit “cancel” threats. Words like “unsafe,” “share,” “breach,” or “GDPR” often pair with negative sentiment and high effort. In my experience, teams miss this because tags are inconsistent and nobody’s checking the raw text at scale. Without structured signals, you argue about outliers and miss the pattern sitting in plain sight.
Why legal‑only workflows fail customers
A legal‑only flow is narrow. It answers “are we compliant,” not “did the customer regain trust.” The gap shows up in silence after the notice goes out. Customers still feel exposed, CSMs still wing the follow‑up, and product still lacks drivers to fix the root cause. You don’t need more apologies. You need evidence that the issue is known, scoped, and addressed.
The real problem: reactive, siloed privacy comms create churn
Churn rises when privacy comms are late, generic, and disconnected from what customers actually experienced. The root cause isn’t one bad email, it’s a system that can’t see patterns early or personalize remediation. Fixing this starts with full conversation coverage, a shared taxonomy, and metrics that trace back to quotes. For example, a “data‑deletion delay” theme appears across tickets weeks before a spike.
Symptom vs cause
Teams point to a missed template or a slow review. The cause is deeper, often that no one owns a cross‑functional privacy signal. Without shared drivers, legal pushes notices, CX handles replies, and product misses why it happened. A shared metric for privacy mentions, tied to drivers, changes the conversation from story to system.
Silos that break the loop
Legal writes. CX explains. Product patches. But the loop never closes because insights aren’t traceable. Leaders ask “how many customers were affected, and what’s their ARR,” and the room pauses. It’s not a messaging problem. It’s a data problem.
The cost of getting privacy wrong: churn, time, trust for Prevent churn from privacy
Privacy mistakes carry hard costs and soft trust debt. Time disappears into manual reviews, ARR walks when high‑value accounts lose confidence, and your team burns cycles on rework. The math compounds. A few missed signals this quarter become a renewal hole next quarter. Think 40 tickets a day, 5 minutes each, and that’s hours lost to guesswork every week.
Time math you can take to finance
If you handle 1,000 tickets a month, sampling 10 percent at 3 minutes each is 5 hours for a partial view. Double it when incidents hit and leaders want “one more pass.” That is just the review time, not the follow‑up with product or legal. It’s the same mistake teams make during spikes, and it burns out your best people.
ARR at risk, by the numbers
Retention beats acquisition on unit economics. Research shows keeping a customer is far cheaper than replacing one, which means privacy‑driven churn hurts more than it looks on a dashboard. A single missed privacy pattern in your top decile of ARR isn’t a nuisance, it’s a forecast change. The Harvard Business Review on retention economics lays out the cost gap clearly.
Trust debt compounds
Consumers punish brands that mishandle data. Cisco’s research shows trust drives purchase and loyalty decisions, which maps directly to churn risk when privacy incidents surface. If customers believe you’re careless, they leave. The fix isn’t silence. It’s evidence and speed. See Cisco’s Consumer Privacy Survey for context.
What it feels like when privacy drives churn
You feel it first in the escalations. Then in the renewal meetings. Late nights rewriting notes that still sound off. You can’t prove scope, so every conversation drifts into opinion. That is the moment when privacy stops being a legal file and becomes a retention crisis. Picture a CSM apologizing without data, and you’ll picture churn, especially when evaluating prevent churn from privacy.
The late‑night scramble
Someone forwards a thread with “urgent.” You dive in. There’s a template, but it’s generic. Customer replies with a specific quote from the agent chat that doesn’t match your note. Now you’re stuck reconciling stories. It’s not that the team did nothing. It’s that nobody linked the metric to the ticket.
The awkward CSM call
You call a high‑value customer. They want proof. Which tickets. Which users. What changed. You have intent, not evidence. That call shapes renewal probability more than any discount ever will. It’s usually avoidable with traceable signals and a plan.
How to prevent churn from privacy with an evidence‑backed playbook
You prevent churn from privacy by turning every relevant conversation into metrics you can trust, prioritizing remediation by value at risk, and measuring the lift. The core is simple. Build a “privacy‑mention” metric in your language, map raw tags to privacy drivers, then test legal‑safe outreach you can prove works. One pilot, one quarter, real results.

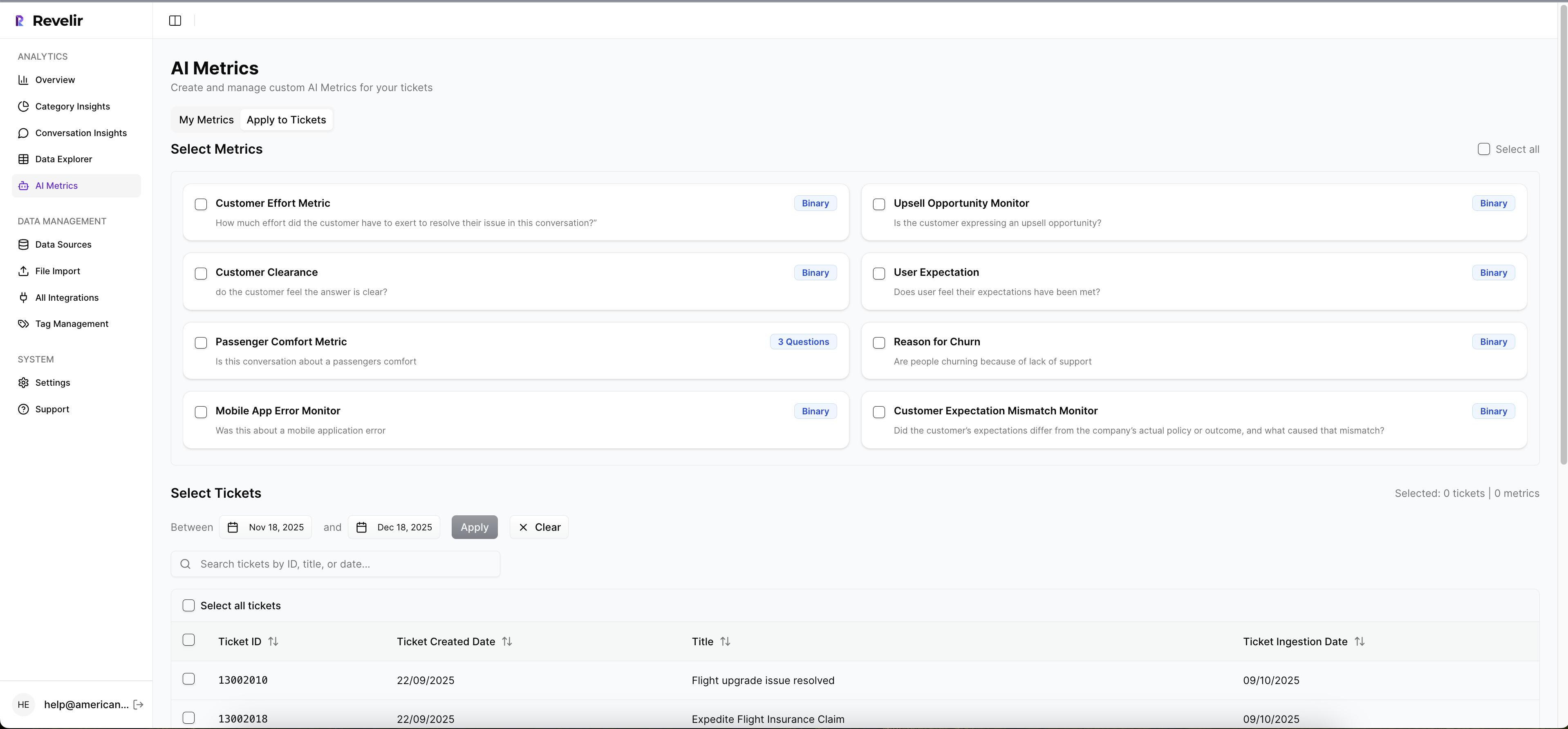
Define a “privacy‑mention” metric in your language
Start by writing the exact question your business cares about, like “Does this conversation mention a privacy concern that could impact trust or retention?” Keep the values simple, for example Yes or No, with optional qualifiers like “breach, data request, policy confusion.” Then validate on a sample of real tickets, side by side, until the detections match human judgment.
When I do this with teams, we read 50 tickets together. We mark what counts, what doesn’t, and why. You’ll find edge cases, and that’s good. Codify them. Nobody’s checking edge cases later unless you write them down now.
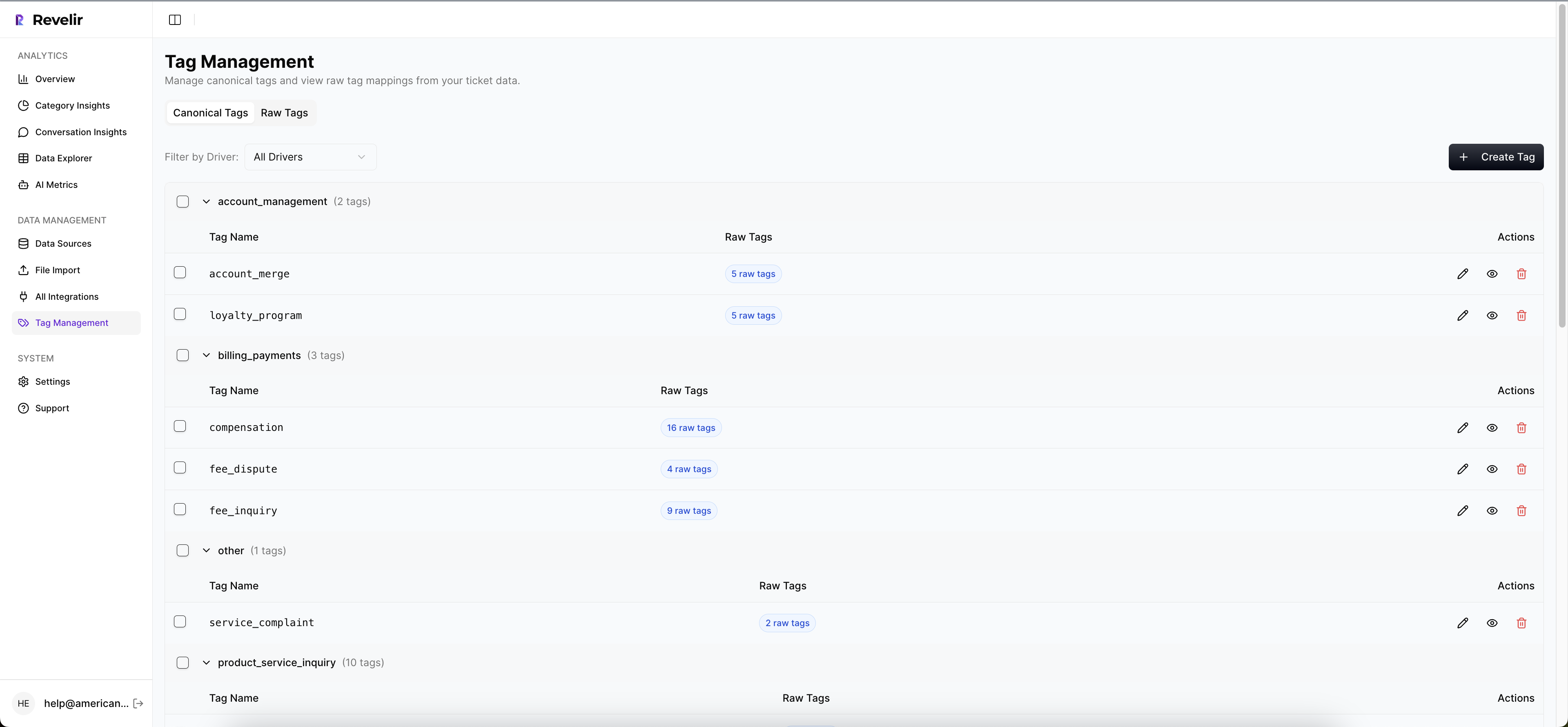
Map raw tags to canonical privacy drivers
Raw tags surface messy, specific phrases like “unsubscribe loop” or “data export delay.” Roll those into canonical drivers that leadership understands, such as Policy Clarity, Access Requests, Data Deletion, or Security. The point is clarity. Drivers answer why privacy issues happen, not just that they happen.
Once mapped, you can group and trend cleanly. It’s the difference between debating a story and showing a stacked chart that links to tickets. Same thing with weekly product reviews. Drivers unlock prioritization.
Prioritize by ARR x sentiment x churn‑risk flag
Not all incidents are equal. Sort privacy‑related tickets by three signals that actually move dollars: account ARR, negative sentiment, and an explicit churn‑risk flag. High ARR plus negative sentiment, plus a Yes on privacy‑mention should jump the queue every time.
A simple prioritization table helps:
- Flag candidates with “privacy‑mention = Yes”
- Filter to negative sentiment or high effort
- Sort by ARR and churn‑risk flag
- Assign owners, due dates, and outreach type
Legal‑safe outreach templates you can test
You don’t need prose art. You need clarity and care. Keep everything factual, avoid admissions, and point to the fix. Run A/B tests on tone and timing, especially when evaluating prevent churn from privacy.
Try three patterns:
- CSM direct note: short, specific, links to help content or next step, optional call
- In‑product banner: scoped to affected cohort, simple status, link to detail page
- Email notice: personalized fields, clear scope, impact window, and support path
For regulatory guardrails, review the EU GDPR breach notification guidance with counsel before launching templates.
Measurement plan that proves it worked
Pick a 60‑day window. Define success as fewer privacy‑driven churn incidents and faster time from incident to remediation. Track three things weekly: count of “privacy‑mention = Yes,” median remediation time, and renewal outcomes for affected cohorts. Compare to the 60 days prior and to a holdout segment if you can.
Also watch leading signals. Negative sentiment on privacy drivers should drift down. CSM notes should include fewer “checking with legal” phrases over time. It’s small, but it’s real.
Stop guessing which privacy issues cause churn. Start triaging with evidence. See how Revelir AI works
How Revelir helps you prevent churn from privacy incidents
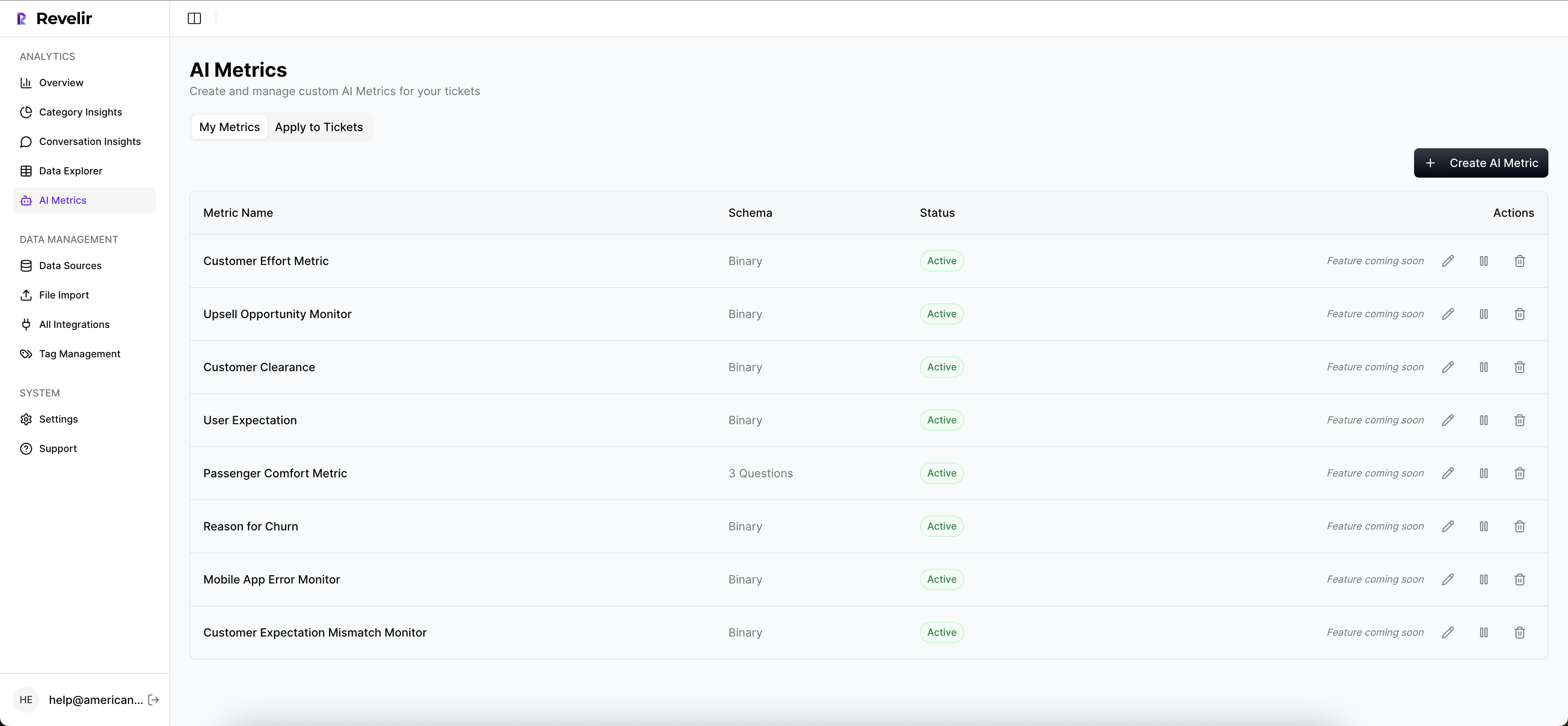
Revelir turns privacy conversations into traceable metrics and drivers, so you can spot risk early, act faster, and walk into reviews with proof. It analyzes every ticket, computes core AI metrics, and links aggregates back to exact quotes. That means less debate, more decisions. Teams use it to prioritize privacy fixes by ARR, sentiment, and churn‑risk in one place.
Full coverage with signals you can trust
Revelir processes 100 percent of ingested tickets, no sampling, so you don’t miss the quiet privacy patterns that often predict churn. The AI Metrics Engine adds sentiment, churn risk, effort, and outcome, while Custom AI Metrics let you define your own “privacy‑mention” in your language. Evidence‑Backed Traceability ties every trend back to the source ticket.
From drivers to decisions in minutes
The Hybrid Tagging System produces granular raw tags and rolls them up to human‑aligned canonical tags and drivers. Analyze Data summarizes metrics by driver or tag, so you see whether Policy Clarity or Access Requests is spiking in negative sentiment among high‑value accounts. Then you click straight into Conversation Insights to validate examples.
Prioritize, validate, and measure impact
Data Explorer works like a pivot table across ARR, sentiment, churn‑risk, drivers, and your custom privacy metric. You filter to “privacy‑mention = Yes,” sort by ARR, and assign outreach paths with confidence. API Export lets you bring structured metrics into your BI stack for leadership reporting. It’s fast, and it’s defendable.
Fewer privacy‑driven churn incidents in weeks. That’s what Revelir delivers. Learn More
Conclusion
Privacy incidents aren’t paperwork. They’re retention moments. When you see every signal, group them into drivers, and tie actions to ARR, you prevent churn from privacy instead of explaining it after the fact. The playbook is straightforward. Define the metric, map the drivers, set the prioritization, test outreach, and measure lift.
If you embed the workflow, the results follow. Within 60 days, you can reduce privacy‑related churn incidents and cut median incident‑to‑remediation time to under 72 hours. Start small, prove it, then scale across segments. That is how you turn privacy from a risk into an advantage.
Revelir’s Custom AI Metrics and Data Explorer handle the heavy lifting so your team can focus on fixes and outreach. Get started with Revelir AI (Webflow)
Frequently Asked Questions
How do I create a custom privacy-mention metric?
To create a custom privacy-mention metric, start by defining the exact question your business cares about, like 'Does this conversation mention a privacy concern that could impact trust or retention?' Keep the values simple, such as Yes or No, and consider adding qualifiers like 'breach' or 'data request.' Once you have your definitions, validate them by reviewing a sample of real tickets to ensure your detections match human judgment. This process helps you capture the nuances of privacy concerns effectively.
What if I need to analyze past tickets for privacy issues?
If you want to analyze past tickets for privacy issues, you can use Revelir's CSV ingestion feature. Export your historical tickets from your helpdesk as a CSV file, then upload it via the Data Management section in Revelir. Once uploaded, Revelir will parse the transcripts and apply its tagging and metrics pipeline, allowing you to explore the data for privacy mentions and related patterns without missing any critical insights.
Can I prioritize privacy-related tickets by churn risk?
Yes, you can prioritize privacy-related tickets by churn risk using Revelir’s Data Explorer. Start by filtering for tickets that have a 'privacy-mention' flagged as Yes. Then, sort these tickets based on churn risk and account ARR. This way, you can focus on high-value accounts with negative sentiment or explicit churn risk signals, ensuring that your remediation efforts are directed where they matter most.
When should I use legal-safe outreach templates?
You should use legal-safe outreach templates when addressing privacy incidents that could impact customer trust. These templates help ensure your communication is clear, factual, and avoids admissions of liability. Try using a direct note from your Customer Success Manager, an in-product banner for affected users, or a personalized email notice. Testing different tones and timings can help you find the most effective way to communicate with your customers during these sensitive situations.
Why does my team struggle to see patterns in support tickets?
Your team may struggle to see patterns in support tickets due to inconsistent tagging and reliance on sampling. Manual reviews can miss critical signals, and without comprehensive coverage, you might overlook subtle trends that indicate churn risk. To address this, consider using Revelir's full-coverage processing, which analyzes 100% of ingested tickets. This approach eliminates bias and allows you to identify patterns and insights that could be crucial for improving customer retention.