7 days is usually all you get. If a bad launch triggered churn-risk tickets this week and nobody checked the ticket evidence fast enough, feature-flag rollbacks happen after the damage, not before it.
Most teams still wait for dashboards, BI cleanup, or a postmortem deck before they reverse a risky release. That sounds disciplined. It isn't. If support is suddenly telling you high-value customers are angry, stuck, or talking about leaving, the feature-flag rollback decision should start there.
Key Takeaways:
- Feature-flag rollbacks work best when you define surge thresholds before launch, not during the incident.
- A useful rollback signal combines three things: churn-risk density, ticket volume, and affected cohort value.
- Scores alone won't tell you what to reverse. Drivers, tags, and ticket evidence will.
- If churn-risk density doubles within 24 hours after release, treat that as a rollback review trigger.
- Safe rollback patterns include kill-switches, gradual rollback, and circuit-breakers tied to support evidence.
- You need pre and post rollback checks to prove causality, or the room will argue about anecdotes.
- The real goal is simple: cut release-driven churn spikes by 30 to 60% inside 7 days.
If you want the short version before we get into the weeds, Learn More. The main thing is this: feature-flag rollbacks shouldn't be treated like engineering embarrassment. They should be treated like retention defense.
Why Feature-Flag Rollbacks Usually Start Too Late
Feature-flag rollbacks start too late because most companies wait for lagging metrics instead of using support conversations as an early warning system. By the time revenue data, renewal analysis, or survey trends confirm the problem, the damage is already spreading across your most fragile accounts. That's why fast rollback decisions need support evidence, not just dashboard confirmation.
The usual playbook sounds smart on paper. Release goes out. Team watches topline metrics. Maybe they wait 48 hours. Maybe longer. Product wants more certainty, support says customers are upset, leadership asks for proof, and everybody stalls because nobody wants to reverse a launch based on what feels like noisy ticket traffic.
At 8:14 AM Wednesday, a PM at a mid-market SaaS company is staring at Slack, Zendesk, and a launch channel that suddenly feels louder than it did on Tuesday. By 2:37 PM, support has logged 46 tickets tied to billing confusion, 14 from larger accounts, and 6 using language like "this broke our process" or "we may need to reconsider." The revenue dashboard still looks calm because renewals haven't moved yet. CSAT barely twitches because only a few customers answered. Same thing with NPS. Too slow. Too abstract. Meanwhile the PM knows the release is live, the queue is filling, and every hour without feature-flag rollbacks increases the odds that one annoyed admin turns into an internal champion for leaving.
The real problem isn't that teams lack data. It's that they trust the wrong data at the wrong time. Support conversations are where the first visible signals show up, especially when the issue is new, sharp, and tied to a release. Think of support like the breaker panel in a data center: the sparks show there first, long before the CFO sees smoke on a revenue report. If your rollback process ignores those signals until BI catches up, you're choosing slow certainty over fast damage control. And yes, I get why teams do it. Nobody wants to look jumpy. But hesitation is expensive.
The hidden lag in score-based decisioning
Three questions diagnose whether your team is already late on feature-flag rollbacks: Are you waiting for CSAT or NPS to move before opening rollback review? Can anyone tie a score dip to one release without reading transcripts? And does your dashboard update slower than support volume spikes? If the answer is yes to two of the three, your rollback process is lagging by design.
Survey and dashboard metrics are summary outputs. They tell you that something happened. They rarely tell you why it happened fast enough to stop it. That's a big distinction.
A drop in CSAT can reflect onboarding friction, billing bugs, slow response times, or three unrelated issues colliding at once. Sentiment trends can point downward without telling you which release caused the drop. If you're trying to decide whether a feature-flag rollback is the right move, the old score stack leaves a gap right where the decision needs clarity. Useful for reporting? Absolutely. Useful for fast containment? Not usually.
Why sampled tickets create false confidence
A support lead reviewing 20 tickets in a calm week can get away with sampling. During a bad launch, that same habit becomes theater.
If a manager pulls the loudest tickets, you overweight drama. If they pull random ones, you might miss the exact cohort that's at risk. The mechanism matters here: release issues rarely spread evenly; they cluster around one workflow, one customer type, one permissions path. So the smaller the sample, the easier it is to miss the cluster that actually justifies feature-flag rollbacks.
My rule is simple: if a launch affected more than 5% of active users or touches billing, onboarding, permissions, or core workflows, don't sample for rollback decisions. Use full coverage or assume you're partly blind. That's not purism. That's risk accounting.
What this feels like in the room
What happens in the incident room isn't confusion. It's a trust vacuum.
Support is escalating screenshots. Product is asking for trend confidence. Data wants one more day. Leadership wants a crisp answer no one can give. And because no one agreed on rollback evidence before launch, the meeting starts inventing standards in real time.
That's the worst part. Not the bug itself. The waiting. So what should actually trigger feature-flag rollbacks before the room burns another afternoon pretending uncertainty is discipline?
The Better Reframe Is Simple: Roll Back on Evidence, Not Scores
Feature-flag rollbacks should be triggered by evidence-backed support signals, not score movement alone. The fastest reliable signal is a surge in issue-specific churn risk tied to a release, especially when the same driver shows up across a defined customer cohort. That changes the rollback conversation from "do we feel nervous?" to "is this release creating measurable retention risk right now?"
This is where most teams have the category wrong. They think rollback decisions are release management decisions. They're not. They're customer risk decisions with a release attached. Once you frame it that way, support data moves from background noise to operational control surface.
I use a simple model for this. Call it the 3D Rollback Test: Density, Driver, Dollar exposure. If all three line up, you don't need a perfect BI read to start rollback review.
Density tells you whether the spike is real
At 12%, the signal is worth a human review. At 20%, you're already inside rollback territory.
Density means the share of affected conversations carrying the same risk signal. Not raw volume alone. Raw volume lies all the time. A launch during peak season will spike tickets anyway.
Start with this threshold: if churn-risk ticket density tied to a release-specific issue rises above 12% of related tickets in 24 hours, trigger human review. If it crosses 20%, prepare feature-flag rollbacks unless evidence clearly says the issue is isolated. Those aren't magic numbers. They're decision numbers. Big difference.
Driver tells you whether the issue has a single cause
Imagine two launches. In one, tickets scatter across slow loading, unclear copy, and account setup friction. In the other, 31 of the last 40 churn-risk tickets mention invoice edits failing after Release X. Same ticket count. Very different rollback story.
Drivers matter because they answer the why question. If the surge is spread across unrelated themes, rolling back one flag may not solve much. If the surge clusters around one driver like Billing, Onboarding, Account Access, or Performance, now you're dealing with a sharper causal story.
That's why "negative sentiment is up" is weak and "Billing confusion among upgraded accounts is driving churn-risk mentions after Release X" is strong. One is a mood. The other is an operating signal.
Dollar exposure forces prioritization
What if the surge is real but concentrated in low-value users? Then you still respond, just not with the same urgency.
Not every painful spike deserves the same response. A surge affecting low-value trial users is different from a surge hitting enterprise admins in renewal quarter. Fair point, some teams hate using account value in rollback calls because it sounds political. That's a valid discomfort. But if feature-flag rollbacks are about retention defense, cohort value has to be part of the math.
A practical rule: if a release-linked driver spike hits accounts representing 10% or more of expansion pipeline, renewal book, or top-tier revenue segment, escalate one level faster than normal. That's the part most teams ignore. Then they act surprised when a "small" bug turns into a board-level problem.
The strongest counterpoint, and why it still doesn't hold
Rollback caution has a real upside. Nobody should pretend otherwise.
Rollbacks can create fresh confusion, technical whiplash, and internal panic. Totally fair. If your architecture is fragile, or your release touched shared dependencies, a hasty rollback can make things worse. There's also a real tradeoff here: the cleaner your rollback discipline, the more product teams must invest in containment paths before launch.
But that's an argument for safer rollback design, not for ignoring evidence. If you can't reverse a risky change inside 72 hours, your release process is missing a containment layer. That's the real issue. So what thresholds separate noise from a true feature-flag rollback call?
The Rollback Thresholds That Actually Reduce False Positives
Good feature-flag rollbacks use predefined thresholds, not gut calls made in the middle of a launch incident. The best threshold model combines three inputs: churn-risk density, ticket volume delta, and cohort concentration. If one metric moves, monitor. If two move, investigate. If all three move together, act.
Most teams fail here because they use one blunt rule. "If tickets go up, roll it back." That's too crude. Ticket volume alone catches noise. Sentiment alone catches frustration without stakes. Churn-risk alone can overreact to a few dramatic conversations. You need a stack.
I call this the 2-of-3 Gate. It keeps you from rolling back every messy launch while still moving fast when the evidence is real.
Start with density, not raw count
If churn-risk density is 1.8x baseline within 24 hours, open investigation. If it hits 2.5x baseline, open rollback review even if the dashboard still looks fine.
Density normalizes the signal. Twenty angry tickets might mean a crisis. Or nothing. Depends on baseline.
Use this baseline structure:
- Measure release-related tickets as a percentage of total tickets in the affected workflow.
- Measure churn-risk flagged tickets inside that same release-related set.
- Compare both numbers to the prior 14-day baseline for the same workflow and cohort.
Before this step, teams stare at raw counts and argue. After this step, the conversation shifts to rate-of-change in a defined workflow. Much cleaner.
Add a volume threshold so tiny samples don't fool you
A scary percentage on six tickets is a mirage. A scary percentage on 80 tickets is an incident.
That's why the second gate is minimum incident volume.
A practical threshold for most teams:
- Below 15 related tickets: watch, don't roll back yet
- 15 to 40 related tickets: investigate and inspect transcripts
- 40 plus related tickets in 24 to 48 hours: qualify for rollback decisioning if density and cohort gates are also hit
Honestly, this is where a lot of teams get tripped up. They see a scary percentage in a tiny set and overreact. Or they see huge raw volume in a broad release and underreact because the percentage looks small. You need both.
Cohort concentration is your anti-noise filter
Contrast broad frustration with concentrated pain. Broad frustration can be support load. Concentrated pain is where feature-flag rollbacks usually earn their keep.
Ask whether the spike is concentrated in a meaningful group: new customers, enterprise admins, recently upgraded accounts, customers on one plan, one region, one integration path. If more than 30% of affected churn-risk tickets come from a single high-value cohort, the chance that you're looking at random noise drops fast.
This matters because real release issues usually break along workflow lines, not evenly across the whole customer base. In other words, releases fail like cracked APIs, not like weather.
Use a red-yellow-black triage band
Green-yellow-red is too polite for rollback work. Use red-yellow-black instead.
- Yellow: 1 gate triggered. Monitor every 6 hours.
- Red: 2 gates triggered. Start incident review and ticket inspection.
- Black: all 3 gates triggered. Prepare or execute feature-flag rollbacks inside the current operating window.
Black sounds harsh. Good. It should. If you're in black and still waiting for next week's dashboard, you're choosing avoidable loss.
The sampling checks you still need
Even a strong threshold model can misread coincidence. That's true. The fix isn't broad debate; it's a narrow validation pass.
Inspect:
- 10 highest-risk tickets
- 10 recent tickets from the affected cohort
- 5 tickets that look similar but came before the release
- 5 tickets from unaffected cohorts, if available
This gives you a 10-10-5-5 check. If the post-release group shows new failure language and the pre-release group doesn't, your causal read gets much stronger. If the language was already there before launch, don't force feature-flag rollbacks just because the room is tense.
Now you've got a trigger system. Next comes the scary part: how do you execute feature-flag rollbacks without causing a second incident?
How Safe Teams Execute Feature-Flag Rollbacks Without Chaos
Safe feature-flag rollbacks rely on preapproved rollback patterns, narrow authorization paths, and post-action validation. You don't want a heroic scramble. You want a boring system that knows when to shut something off, who can approve it, and how to prove the rollback worked. That's what keeps a risky launch from turning into a long retention leak.
This is where people confuse caution with slowness. Safe doesn't mean slow. Safe means constrained. The release already created uncertainty. The rollback process should remove it.
There are three rollback patterns that matter most. Use the one that matches blast radius and confidence level.
Kill-switch for obvious high-risk failures
If churn-risk density is above 20%, affected volume is above 40 tickets, and cohort concentration is above 30% in a high-value segment, default to full off.
Use a kill-switch when the evidence is sharp, concentrated, and tied to a clearly bounded feature. Billing flows. Onboarding blockers. Permission changes. Anything that breaks trust fast.
The downside is obvious. You can interrupt users who weren't hit. That's real. But when the issue is severe and localized to one release path, kill-switches are often the cleanest move. Boring beats brave here.
Gradual rollback when causality is strong but not complete
A regional rollout gone sideways rarely needs an all-at-once reversal. Sometimes the smartest feature-flag rollback is a partial retreat.
Maybe the issue only hits one region or plan tier. Maybe support language points to two possible causes. That's where gradual rollback works.
Reduce exposure in steps:
- Turn the feature off for the highest-risk cohort first
- Monitor churn-risk, sentiment, and customer effort for 6 to 12 hours
- Expand rollback if the signal persists
- Pause if the signal drops and ticket language changes
This gives you a cleaner causal read without forcing an all-or-nothing choice.
Circuit-breaker rules for repeat patterns
What do you do when the same class of launch keeps blowing up the same workflow? Stop pretending each incident is unique.
Build a circuit-breaker rule. Example: any new release touching checkout or plan management automatically enters rollback review if churn-risk density doubles and customer effort turns high within 24 hours. That way the trigger is operational, not political.
Gone is the theater where every feature-flag rollback has to be argued from scratch. Repeated failure modes should have repeated containment logic.
The authorization flow that prevents drift
Three people is enough for most rollback decisions.
Nobody wants six approvers on a rollback thread. You need one decision owner, one technical executor, one support witness. That's enough for most cases.
A clean flow looks like this:
- Support or CX opens incident review when threshold hits red
- Product owner confirms release scope
- Engineering lead executes rollback at black, or earlier with agreement
- CX validates transcript changes and cohort response after rollback
I prefer a 15-30-120 rule here:
- 15 minutes to confirm the signal
- 30 minutes to choose rollback pattern
- 120 minutes to execute and communicate
Longer than that and you're drifting.
Post-rollback proof matters more than the rollback itself
Plenty of teams celebrate the reversal. Very few prove it worked.
If you don't validate after feature-flag rollbacks, the organization learns nothing and the same release class bites you again.
Track these four checks within 24 hours:
- churn-risk density change
- sentiment shift in the affected driver
- customer effort change where supported
- new ticket language versus pre-rollback language
You need those checks because the final job isn't just to reverse damage. It's to turn the rollback into a prevention asset. And if the proof is weak, the next section matters even more: where do you get evidence people will actually trust?
Why Revelir AI Gives Rollback Decisions Real Evidence
Feature-flag rollbacks get faster and more defensible when the support signal is structured, searchable, and tied back to real tickets. Revelir AI does that by turning messy conversations into evidence-backed metrics, drivers, and tags you can inspect instead of argue about.
Revelir AI sits on top of the support data you already have, through Zendesk Integration or CSV Ingestion, and processes 100% of those conversations. With Full-Coverage Processing, you're not trying to infer a pattern from a tiny slice.
Drivers and custom metrics make support patterns clearer
Basic sentiment is a weather report. Driver-level evidence is a radar screen.
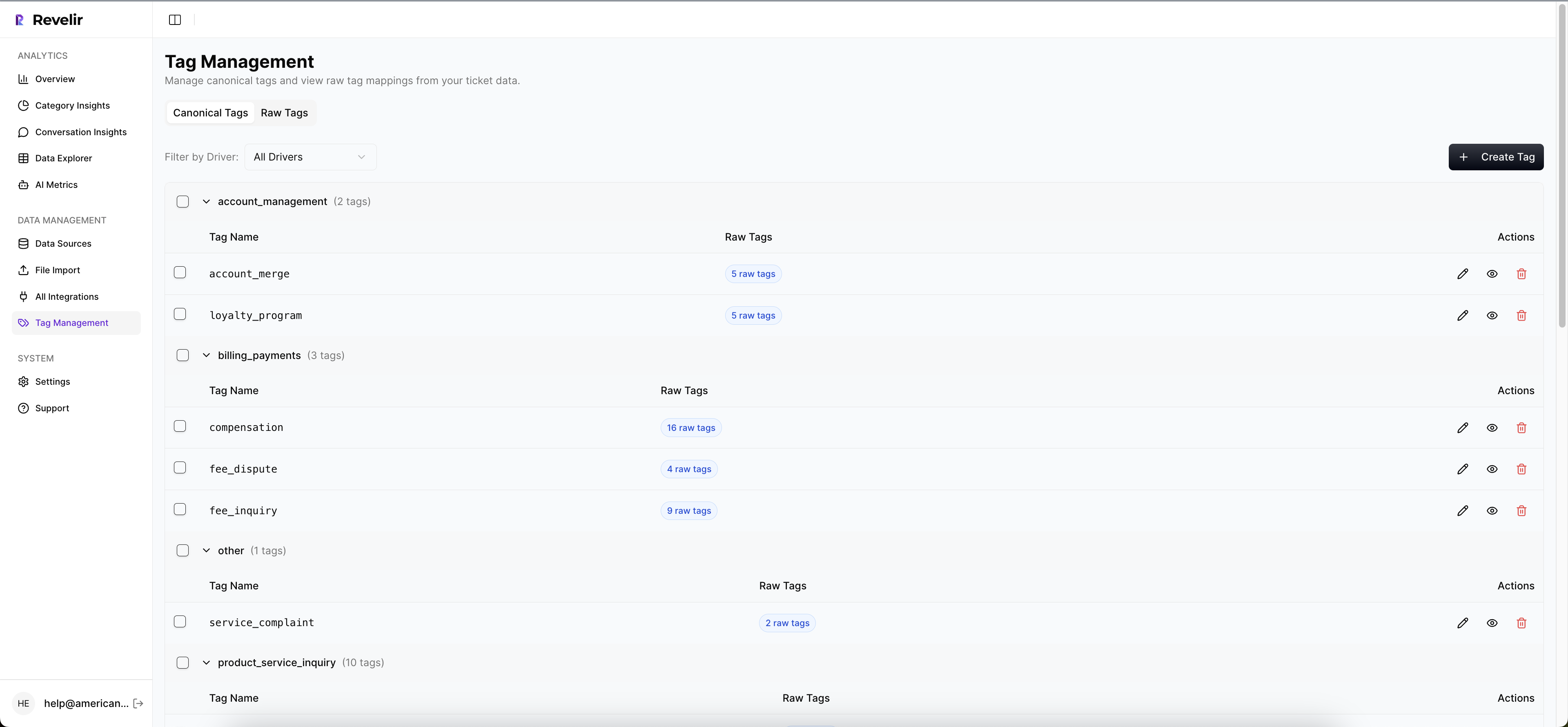
Basic sentiment can tell you customers are upset. It can't tell you whether the issue is billing confusion, onboarding friction, or permission failure in language your business actually uses.
Revelir AI uses a Hybrid Tagging System with Raw Tags and Canonical Tags, plus Drivers, so teams can move from "something feels off" to a clearer view of the themes showing up in support conversations. On top of that, Custom AI Metrics let you define your own business-specific classifiers. If your team needs a metric like migration_blocked, onboarding_stuck, or pricing_confusion, you can create that and use it alongside Sentiment, Churn Risk, Customer Effort, and Outcome in the AI Metrics Engine.
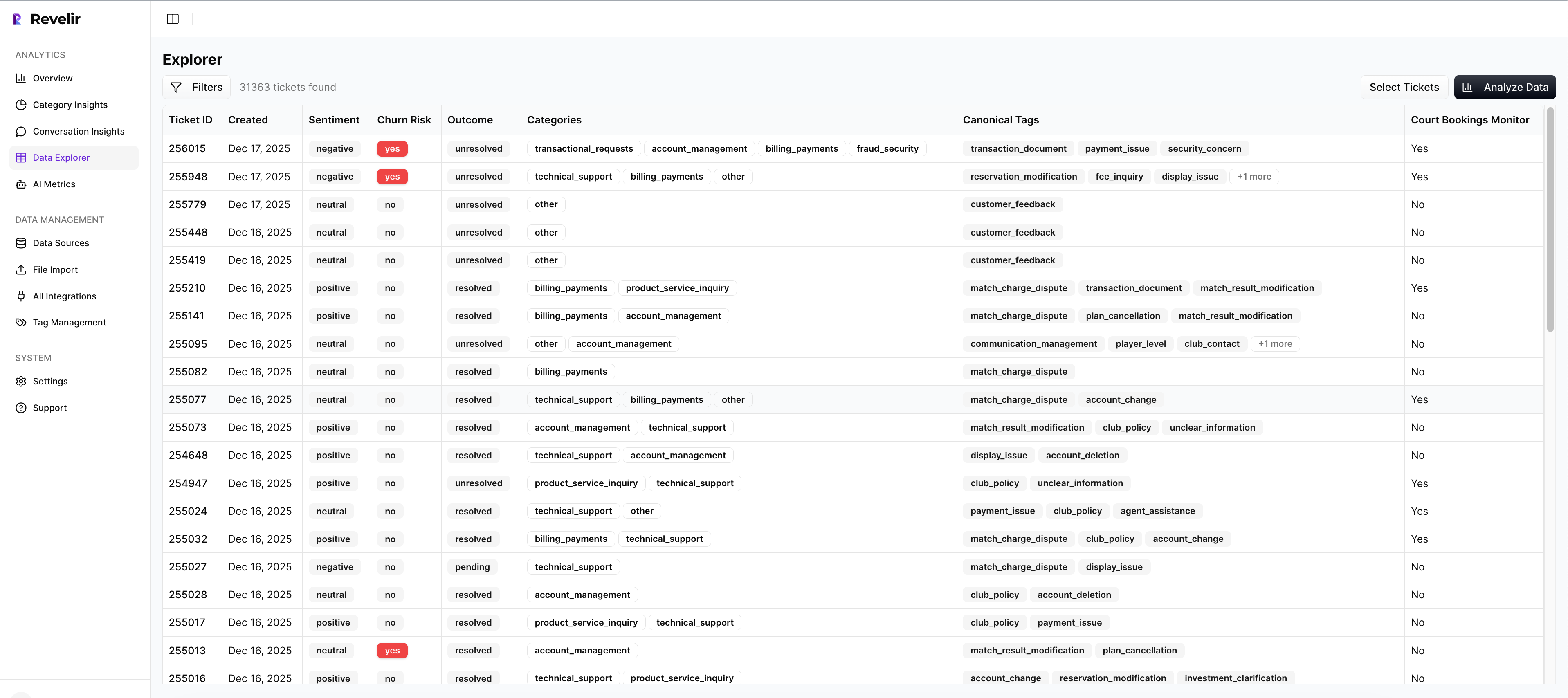
Data Explorer and traceability make analysis easier to defend
Once a spike appears, the next fight is always proof. Revelir AI's Data Explorer gives you a row-level workspace to filter, group, and inspect tickets by churn risk, effort, tags, drivers, and custom metrics. Analyze Data summarizes those signals by dimensions like Driver or Canonical Tag, then links the output back to underlying tickets.
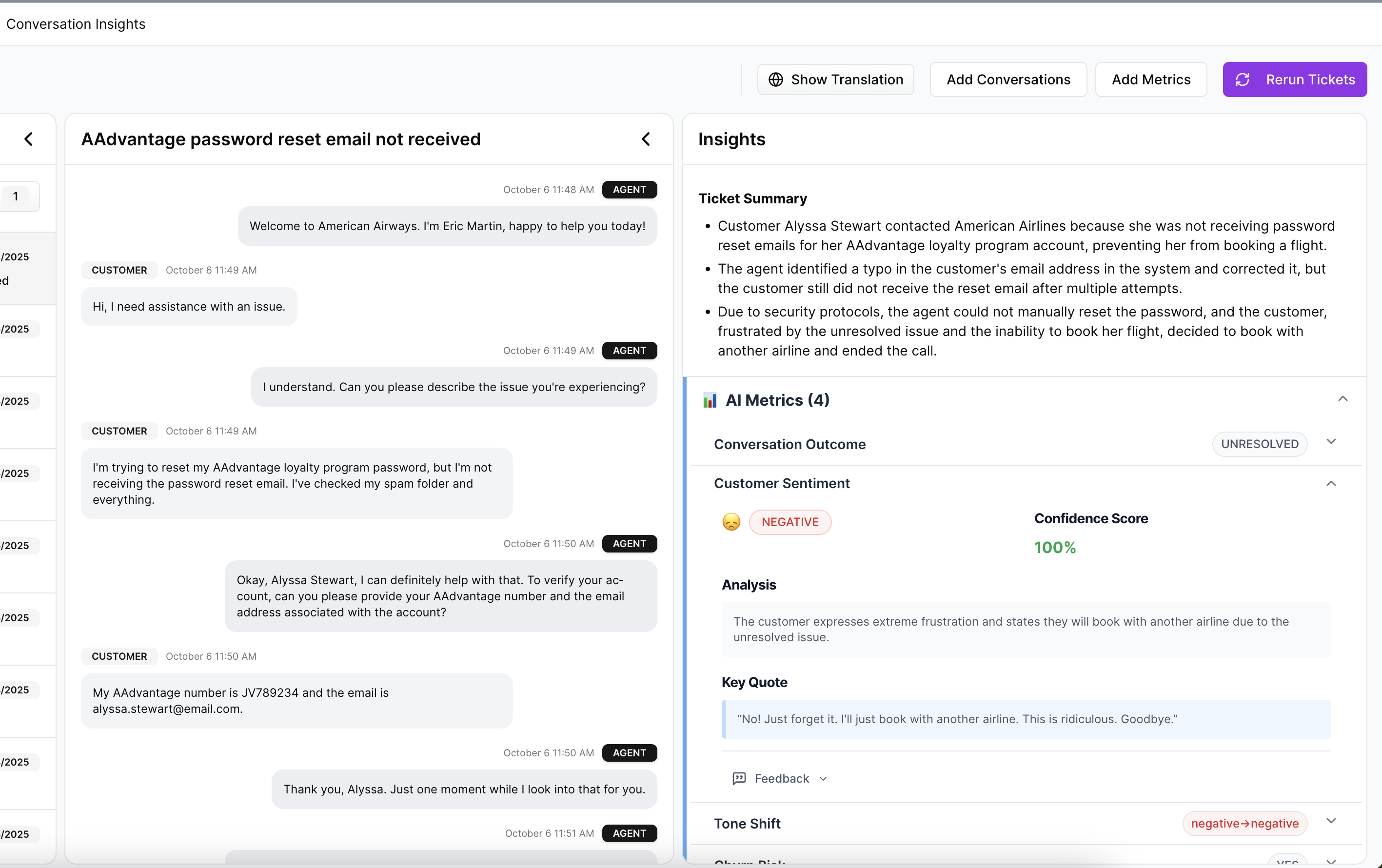
That's a big deal. Evidence-Backed Traceability means every number can be tied back to the source conversations and quotes. Conversation Insights lets teams drill into transcripts, summaries, tags, drivers, and metrics to validate patterns and gather quotes for reporting. Same thing with leadership reviews. The conversation changes when you can show the metric and the exact tickets behind it.
If the goal is faster, calmer feature-flag rollbacks, structured evidence beats louder opinions every time.
Make 72 Hours the Standard, Not the Aspiration
Feature-flag rollbacks should be treated like a retention control, not a last-resort engineering admission. If support evidence shows a release is driving churn-risk concentration in a high-value cohort, waiting for lagging metrics is usually the bigger mistake.
The better operating model is pretty clear. Define thresholds before launch. Use the 2-of-3 Gate. Validate with focused ticket checks. Execute kill-switch, gradual rollback, or circuit-breaker patterns based on severity. Then prove the reversal worked with post-rollback evidence.
That's how you reduce the size of churn spikes tied to new releases by 30 to 60% inside 7 days. And if the team is serious, set the real standard: a 72-hour detection-to-rollback SLO for high-risk launches. Because once customers start telling you what's broken, the clock is already running.
Frequently Asked Questions
How do I set up Revelir AI for ticket analysis?
To set up Revelir AI for ticket analysis, start by integrating it with your support platform like Zendesk. This allows Revelir to automatically ingest all your support conversations. Next, use the Data Explorer feature to filter and group tickets based on key metrics like churn risk and sentiment. This setup helps you analyze trends and identify issues quickly, ensuring you can respond effectively to any spikes in churn risk.
What if I notice a sudden spike in churn-risk tickets?
If you notice a spike in churn-risk tickets, first check the churn-risk density using Revelir's Data Explorer. If it exceeds your predefined threshold, initiate a rollback review. Use the Analyze Data feature to summarize the metrics and identify common drivers behind the churn. This evidence-based approach allows you to make informed decisions about whether to roll back a feature or address specific issues.
Can I customize metrics in Revelir AI for my specific needs?
Yes, you can customize metrics in Revelir AI using the Custom AI Metrics feature. This allows you to define specific classifiers relevant to your business, such as 'billing confusion' or 'onboarding issues.' Once set up, these metrics can be used alongside existing metrics like churn risk and sentiment, giving you a tailored view of your support data that aligns with your operational needs.
When should I consider a gradual rollback instead of a full rollback?
Consider a gradual rollback when the churn-risk density is high but the evidence isn't fully conclusive. Use Revelir AI to identify which customer cohorts are most affected. Start by rolling back the feature for the highest-risk group first, then monitor the impact before expanding the rollback. This method allows you to mitigate risk without disrupting all users at once, making it a safer approach.
Why does my team need to use full coverage processing?
Using full coverage processing is essential because it ensures that all support tickets are analyzed, not just a sample. Revelir AI processes 100% of ingested tickets, which eliminates blind spots and biases that can occur with sampling. This comprehensive analysis allows your team to identify churn risk signals accurately and respond proactively, rather than relying on incomplete data.